BULLZIGA Managed SIEM
Managed SIEM for Modern Threats
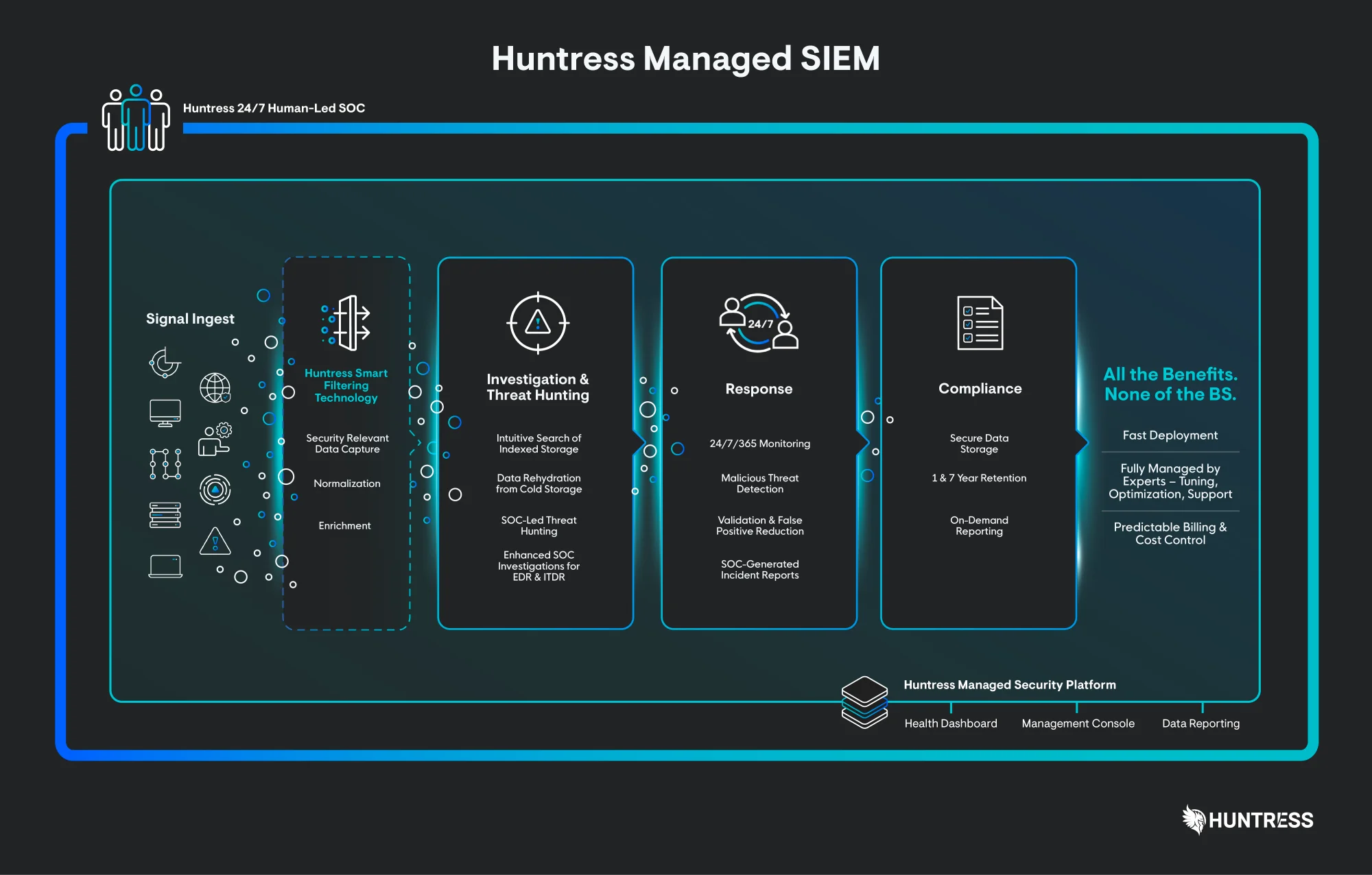
BULLZIGA makes enterprise-grade SIEM accessible to every team with its managed solution. Stay compliant and respond to threats faster with our 24/7 AI-assisted SOC without the complexity, high costs, or challenges of traditional SIEM systems.
24/7 AI-Assisted Threat Protection
BULLZIGA combines AI with human expertise to monitor your environment around the clock detecting, investigating, and stopping threats while ensuring compliance.
Audit-Ready SIEM by
Design
Sleep easy and take control of compliance with powerful search, effortless reporting and long-term data retention up to seven years to meet the most demanding regulatory standards.
Predictable Pricing, No Surprises
Say goodbye to hidden fees and complex tuning. BULLZIGA SIEM gives you full visibility, 24/7 AI-assisted SOC support, and compliance reporting all at a single, transparent rate.
Focused SIEM, No Noise
BULLZIGA SIEM skips log hoarding and focuses on actionable, compliant data. Our Smart Filtering highlights what matters, giving you faster insights, quicker responses, and clean, focused security powered by your 24/7 BULLZIGA SOC.
We handle SIEM, you focus on what matters
Fast Threat Response
BULLZIGA Managed SIEM protects you by tackling threats early in the attack chain. Our SOC experts provide detailed incident reports and can remediate confirmed threats on your behalf.
Investigation & Threat Hunting
BULLZIGA’s human-led SOC monitors your environment 24/7, identifying known malicious activity and hunting for specific threats like RDP brute force attacks.
Total Compliance
Collect relevant log data from endpoints, firewalls, VPNs, identity systems, and more. All data is encrypted in transit and at rest, with storage available for up to seven years.
Fully Managed
BULLZIGA SOC experts monitor, triage, and investigate events around the clock. We fine-tune detections, eliminate false positives, and respond to confirmed threats on your behalf.
Predictable Pricing
BULLZIGA Managed SIEM charges by data source with a pooled allocation, ensuring consistent, budget-friendly pricing without unexpected spikes.
Smart Filtering
BULLZIGA’s proprietary Smart Filtering Engine identifies the data that matters, eliminating noise and keeping costs low so you focus only on what’s important.
Top Mistakes First-Time SIEM Buyers Make
Industry-Disrupting SIEM
Managed SIEM Datasheet
Built for the hunt, priced for protection. Discover how BULLZIGA Managed SIEM eliminates the complexity, noise, and high costs of traditional SIEMs delivering rapid threat response and stronger compliance, fully managed by 24/7 SOC experts at a predictable price.
Securing Businesses Like Yours




SIEM FAQs
What is SIEM?
Security Information and Event Management (SIEM) is a security platform and approach that collects logs and security events from across your environment endpoints, firewalls, VPNs, identity systems, cloud platforms, and more—and centralizes them for storage, search, and analysis of security-relevant activity.
Originally, SIEM was designed to gather multiple log sources under one platform. Correlation rules were added to generate alerts from the collected data. Traditionally, SIEM focuses on log collection and storage, compliance, and threat visibility. However, the “collect all data” approach often leads to high costs, requires skilled staff to manage, and makes it challenging to distinguish useful information from noise.
What is BULLZIGA Managed SIEM and why is it different?
BULLZIGA Managed SIEM delivers powerful threat response and robust compliance support without the large budget, big team, or headaches of traditional SIEMs. Our solution sets a new standard by applying Smart Filtering at the log source, capturing only threat-relevant logs to simplify threat discovery and data retention.
It collects Windows events and syslog through the same proprietary agent you know, while our secure AWS backend safely stores your data. BULLZIGA’s Smart Filtering engine reduces data volume and false positives, keeping only security-relevant events for effective threat hunting and investigations.
Paired with a 24/7 human-led SOC, we write and tune detections, monitor telemetry, triage suspicious activity, and deliver clear, actionable incident reports giving you true managed detection and response, not just a raw log bucket to manage yourself.
Why do I need SIEM protection? Aren’t firewalls and antivirus enough?
Traditional firewalls and antivirus alone aren’t enough on average, it takes six months to discover incidents. Quickly finding and stopping attackers requires a complete view of your log data. SIEM provides this bird’s-eye view, using correlation analysis and Smart Filtering to trace attacker activity across your environment.
While firewalls, antivirus, and even EDR or MDR focus on specific endpoints or network points, many attacks first appear in logs that these tools don’t fully capture. Managed SIEM unifies events from endpoints, identity systems, network devices, and SaaS platforms, helping you spot initial access, lateral movement, and data exfiltration earlier and with more context than endpoint telemetry alone.
It also offers centralized log retention and search features auditors, regulators, and cyber insurers increasingly require so you can prove that critical security events are recorded, searchable, and correlated instead of siloed or quickly overwritten.
What is Smart Filtering and Do Other Vendors Use It?
BULLZIGA designed Smart Filtering from the ground up. Unlike most vendors that rely on the source (firewall, endpoint, router) to filter logs, our proprietary engine directly processes log data acting like a sieve to capture only critical security events.
Smart Filtering reduces SIEM noise and storage needs by discarding routine or low-value logs, keeping only events that matter for detection and investigation. After logs are collected from Windows systems, syslog, or cloud/SaaS integrations, Smart Filtering ensures only relevant data is stored avoiding the “data hoarding” common in legacy SIEMs and enabling long-term retention without runaway costs.
While some vendors offer source-side filtering or rule-based suppression, BULLZIGA’s Smart Filtering is centrally maintained and works across multiple log sources. This is a key reason we can provide predictable per-data-source pricing while keeping alert volumes and false positives low.
What integrations does BULLZIGA Managed SIEM support?
BULLZIGA Managed SIEM works with the IT and security tools your organization already uses, providing centralized visibility across endpoints, network infrastructure, cloud platforms, identity systems, and third-party security controls without a full rip-and-replace.
Windows Event Logs from servers and workstations are collected via the BULLZIGA agent, which also functions as a syslog collector for firewalls and network devices. All logs are Smart-Filtered to retain only security-relevant events, securely stored in BULLZIGA’s AWS backend, and made searchable for threat detection, investigations, and compliance reporting.
Beyond core log collection, BULLZIGA supports third-party EDR sources such as CrowdStrike Falcon, Cisco AMP/Secure Endpoint, and SentinelOne, identity integrations like Microsoft 365, Entra ID, and Duo, as well as cloud and infrastructure logs from AWS CloudTrail, S3 buckets, DNS, and network security platforms like Cisco Umbrella. Operational tooling like NinjaOne is also supported, with integrations enabled through native connectors, APIs, syslog, or HTTP event collectors.
BULLZIGA continuously expands integrations while maintaining Smart Filtering to reduce noise, control data volume, and keep costs predictable as your environment grows.
What are the differences between BULLZIGA Managed SIEM and Managed EDR?
BULLZIGA EDR focuses on rapid, endpoint-level response, while Managed SIEM collects Windows events and syslog data for centralized analysis and long-term storage. SIEM data is hosted by BULLZIGA for one year by default, with options to extend up to seven years for compliance.
While EDR and SIEM work together, they address different parts of the attack surface. EDR answers, “What is happening on this machine right now?” whereas SIEM shows, “What has been happening across the environment over time?” Managed by the same SOC, they complement each other, providing deep host-level visibility alongside broad environmental context.
Do I need a dedicated security engineer to run BULLZIGA Managed SIEM?
No. BULLZIGA Managed SIEM is designed so MSPs and IT teams don’t need an in-house SIEM engineer or standalone SOC. The BULLZIGA SOC handles the heavy lifting designing and updating correlation rules, maintaining Smart Filtering, monitoring telemetry 24/7, investigating suspicious activity, and escalating only meaningful incidents with clear remediation guidance.
Your role is mainly to decide which customers and log sources to onboard, follow SOC guidance for third-party systems like firewalls and VPNs, and run ad-hoc or scheduled queries when needed for reporting or internal investigations.
Is BULLZIGA Managed SIEM easy to deploy for MSPs?
Yes. BULLZIGA Managed SIEM is built for MSPs to deploy quickly and consistently across multiple clients without complex projects or specialized SIEM expertise.
Deployment begins by installing or confirming the BULLZIGA agent on the Windows servers and workstations to monitor. The same lightweight agent collects Windows Event Logs and, if needed, acts as a syslog collector for network devices.
From the portal, you enable Windows Event Log collection for selected hosts, designate syslog collectors, and point supported firewalls and appliances to them. Cloud and SaaS integrations like Duo, DNSFilter, NinjaOne, or SentinelOne can be added via native connectors or an HTTP event collector. MSPs usually start with their own environment and a small pilot group, then scale SIEM across clients using repeatable portal configurations for controlled, predictable deployment.
How noisy is SIEM, and what happens when BULLZIGA detects something?
BULLZIGA Managed SIEM produces far fewer raw alerts than traditional SIEMs, thanks to Smart Filtering and SOC-driven triage. Non-security-relevant noise is removed at ingestion, and the SOC investigates suspicious events, escalating only those that pose real risk reducing false positives and alert fatigue.
When a real issue arises, it appears as a clear incident in the BULLZIGA portal, detailing what happened, which data sources were involved, the likely impact, and recommended or completed actions.
Solving the SIEM Problem
Don’t settle for a SIEM that doesn’t meet your needs it’s time for a fresh approach.
If you’re facing excessive false positives, lacking the right expertise, or dealing with unpredictable costs, BULLZIGA delivers the insights you need to make informed, confident decisions about your security strategy.